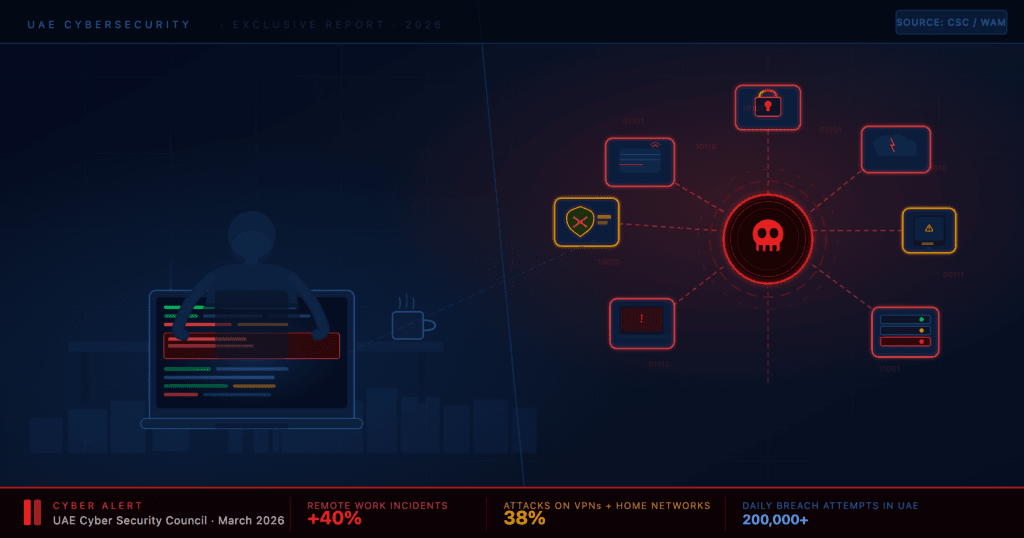
The UAE Cybersecurity Council has issued a fresh warning about the growing threat posed by remote and hybrid work arrangements, saying cyber incidents tied to home-based working have risen by more than 40 per cent in recent years.
The Council, speaking to the Emirates News Agency WAM on Saturday, said the shift to remote work has driven a notable increase in attacks targeting unsecured home routers — vulnerabilities that can expose the data of individuals, institutions, and entire businesses to breaches.
The timing isn’t accidental. The alert comes just weeks after the Council confirmed it had foiled a series of organised, AI-powered cyberattacks targeting the country’s critical digital infrastructure — attacks described as “terrorist in nature”.
The numbers behind the warning
According to the Council, 92 per cent of cybersecurity experts now believe remote work heightens the risk of breaches, largely due to reliance on unsecured home networks and personal devices. Approximately 38 per cent of recent attacks specifically target remote work infrastructure — home routers and VPNs — to intercept communications or steal credentials.
That’s not a marginal risk. Nearly four in every ten attacks are now going through the same network your router sits on.
The problem compounds quickly: according to SonicWall’s 2025 Cyber Threat Report, 61 per cent of hackers exploit new vulnerabilities within 48 hours of public disclosure. In the UAE, the Cyber Security Council has also reported that 50 per cent of local system vulnerabilities are more than five years old — meaning attackers don’t even need sophisticated tools. They just need patience and a target with an unpatched router.
Why home networks are the new frontline
There’s a structural reason for all of this. Corporate offices have firewalls, IT teams, controlled access, and monitoring systems. Home setups have… a router from your ISP and a laptop your company issued two years ago.
The Council said this reflects a deliberate, strategic shift by hackers — moving away from hardened central systems and toward exploiting home environments, where defences are typically weaker and oversight is minimal.
The attack methods vary. Authorities noted that attackers frequently exploit vulnerabilities in personal devices and unsecured networks, redirecting users to fraudulent websites or compromising login credentials through intercepted communications. In many cases, the employee doesn’t even know it’s happened until the damage is done.
Meanwhile, the tools being used against remote workers have become far more sophisticated. AI-powered phishing attacks have emerged as one of the most significant threats in 2025, using artificial intelligence to craft highly personalised and convincing emails that bypass traditional security filters. These aren’t the misspelled, obviously fake messages of a decade ago. Some impersonate executives with near-perfect accuracy.
What the Council is telling workers and businesses to do
The Council’s advisory wasn’t only a warning. It came with specific, actionable guidance — the kind that’s easy to ignore until it’s too late.
The Council advised individuals to delete untrusted applications, enable two-factor authentication, and ensure that operating systems and software are updated regularly. It also cautioned against using open or free Wi-Fi networks for sensitive activities, noting that such networks are frequently unsecured and easily breached.
For those working remotely, the specific recommendations go further: Use only corporate-approved or trusted VPN services when connecting to work systems. Don’t use personal devices for work tasks unless they’re enrolled in your company’s device management programme. And don’t store work credentials in your browser or on personal accounts.
The Council also urged users to avoid storing sensitive passwords on inadequately secured devices and to regularly review privacy settings on personal electronics.
If something looks suspicious — a strange email, an unusual login alert, a link you weren’t expecting — report it. Don’t click first and wonder later.
Suspected cyber incidents in the UAE can be reported through the eCrime portal at ecrime.ae, or via Dubai Police’s Aman service.






